The OSMST (Open Source Magnetic Stripe Tool) is a tool designed to allow security analysts the ability to inexpensively test magnetic stripes and the readers associated with them. It also allows pentesters the ability to do certain tests without having a computer. It is all open source so it also works well as an educational project for anyone who is interested in magnetic stripe technology. Using the schematics and source, it allows one to make a reader, writer and generic test tool that surpasses most commercial products in many ways.
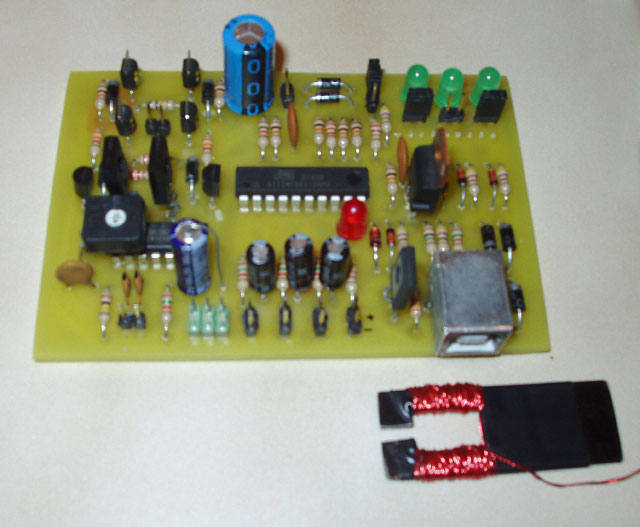
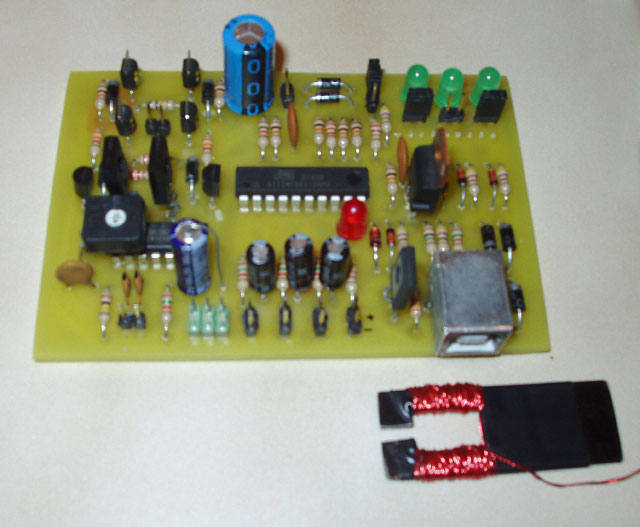
The board PDFs, firmware and construction specifications are included to make it easy to construct. Instructions on the full constrction are included and are designed to make the device easy to assemble from parts that you probably already have if you do any electronics work already. The device was designed with being a project in mind, as such it uses things that should be easy to acquire if you don't already have them. It uses single layer through-hole circuitry, so anyone with a laser printer, some gloss paper, some copper clad board, etching solution and a drill with a small bit should be able to make it easily. With the schematic, it can easily be converted to double sided PCB with SMD components to make it more compact, if you have everything needed to do it. A PC is not required for operation, but is required for the initial programming of the AVR ATTiny861 processor using the onboard standard 6 pin ISP header.
Using the random fuzzing interfaces and the computer upload, you can test access control, ID and data storage systems for flaws. Too frequently systems are assumed to be safe, with the expectation that users cannot easily enter arbitrary data into the system. There are systems that are vulnerable to random data attacks, buffer overflows and SQL injection over the Magnetic Stripe standard stripes. Since the standard stripe character set includes the single-quote character, and several other characters that make SQL injection possible, it allows for attacks like the ' AND 1=1;-- attacks over credit card stripes. Any access control systems that use a 6-bit character set track, or have a decoder that automatically decodes tracks based on bit content and not track position and doesn't properly escape or test incoming track data when passing data to an SQL database may vulnerable to this type of attack.
You can use this device to:
Read magnetic stripes, one stripe at a time.
Play stripe track data to a speaker or recorder.
Emulate track data to an emulator - the one shown in the picture above works at a distance of 3/8" to 1/2" from a few test read heads, at 1/4 max amperage.
Write cards, one stripe at a time. Verification of card data.
Fuzz access systems that work on standard biphase encoding, and store the random fuzz string.
Upload and download from the device EEPROM, which can hold up to 4 single stripe tracks. This allows storage of tracks for emulating or writing later, or temporary storage of stripe data for transfer to a computer or writing to a different card.
Read/Write/Emulate/Fuzz remotely, a computer is not needed for operation
Everything in the project was created with publicly available knowledge on the stripe standards and technology from the web.